Latest Cyber Security News
IoT Security Testing Services
Threat Exposure
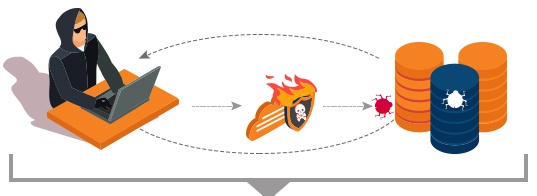
SQL Injection
SQL Injection (SQLi) is one of the oldest, most prevalent and most dangerous vulnerability. In this type of injection attack, attacker executes malicious SQL statements through web forms that control a web application’s database server.
-
Impact
- Access sensitive data from application database
- Can insert, update or remove data from database
- Attacker can execute database administration operation which can lead to shutdown of DBMS
- Opens access to DBMS file system which can result in sharing of sensitive information
- In severe cases, it can open access to operating system commands
-
Testing Recommendations
- Test by inputting special characters like -- (double-hyphen), ; (semicolon), ‘ (single quote), “ (double quote) and other similar characters of special meaning in different flavors of SQL
- Append universally true expressions like 2>1, at the end of all valid input fields using different expressions coupled with a variety of SQL keywords like AND, OR, UNION etc, to simulate an attack
- Useful Tools: Sqlmap, SQLi Dumper
Evaluation – Tools and Technologies

BlackArch Linux is an Arch Linux-based penetration testing distribution for penetration testers and security researchers.

Features
- Derived from ArchLinux
- Can install BlackArch components individually or in groups
- Offers over 1900 tools organized by category, for security, and forensic
- Can be used as a standalone live CD or live USB, run from a virtual machine, or be installed to a computer's hard disk
Key Takeaway
AIEngine - AIEngine is the next generation network intrusion detection engine. This interactive packet inspection engine offers features such as DNS domain classification, spam detection, network collector, network forensics, and many others. What’s more interesting about AIEngine is that it has the ability to learn without any human intervention.
Have Suggestions?
We would love to hear your feedback, questions, comments and suggestions. This will help us to make us better and more useful next time.
Share your thoughts and ideas at knowledgecenter@qasource.com




