Companies are aware that they need to identify any security vulnerabilities present in their products early on in the process, which is why SAST and DAST are quickly becoming integral parts of software development processes.
-

Static Application Security Testing (SAST)
It is a type of white-box testing that requires access to the source code in order to function correctly. SAST can identify various types of security vulnerabilities, including software flaws and weaknesses such as input validation, stack buffer overflows, and SQL injection. SAST does not require a running system to perform assessments and works as an extensible security testing method.
-

Dynamic Application Security Testing (DAST)
It is a type of black-box testing where tests are performed from outside a functioning application. An application or software is validated in its running state when the application has gone into production or entered runtime. Testers follow a hacker's approach in order to find out different security vulnerabilities missed by other testing techniques.
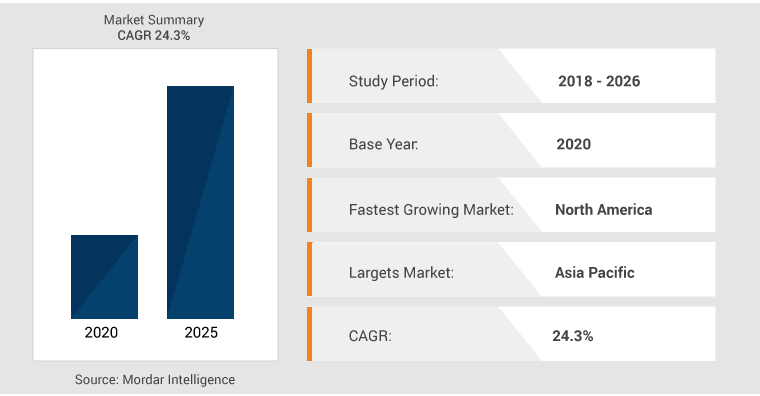
SAST and DAST Trends
- A report by Mordor Intelligence reveals that DAST market will reach a CAGR of 24.3% during 2021-2026.
- A report by IndustryARC reveals that DAST market is forecast to reach $455 million by 2025.
- The rise in DevOps deployments has enabled teams to integrate DAST solutions into the SDLC. This further increased the applicability across industries like healthcare, banking, and education.
- Due to the rise of mobile applications and support towards complex environments, cloud-based security is contributing majorly to static application security.
Difference Between SAST and DAST

-
SAST
- Type of white-box security testing
- A developer's approach to testing
- Deployed application is not required
- Fixing vulnerabilities is cost-effective because testing is performed in the early stages of the software development life cycle (SDLC)
- Discovering issues related to run time and environment is not possible
- Supports all types of software like web applications, web services, and thick clients
-
DAST
- Type of black-box security testing
- A hacker approach to testing
- A running application is required
- Expensive to fix vulnerabilities as they are discovered at the end of the SDLC
- Can reveal issues related to run time and environment
- Supports web applications, mobile applications, and web services only
How To Choose SAST and DAST Tools?
We should consider these factors while comparing different SAST and DAST tools:
False Positives
Look for the data and stats that indicate false positives encountered by users, and analyze how easy or difficult it is to manage these false positives when they occur.
IDE Integration
Analyze each tool to make sure it integrates with your existing development environments. It will impact how your team uses development and security testing methods and show how disruptive testing is to the SDLC.
Automation
Analyze the extent to which static testing can be automated within the development environment. Traditionally, SAST has been considered a manual application security testing method, and hence its automation can improve efficiency conclusively.
SAST Tools
- SonarQube: Organizations all over the world use this tool to own and update code quality and code security.
- Checkmarx CxSAST: Helps in checking errors in the source code. Also detects issues with security and regulation compliance.
DAST Tools

-
- ZAP: An open-source DAST scanner that supports scanning with a desktop application and automated scanning via API.
- Burp Suite: One of the widely used penetration testing tools by security testing teams that perform manual scans.
- HCL Appscan: Formerly called IBM Security AppScan Standard, this tool is a combination of DAST and SAST that can scan over a million lines of code per hour.
QASource can be a go-to partner to help your team choose the appropriate SAST and DAST tools that are most suitable for your application’s requirements. Contact QASource today to manage your security testing needs and compliance requirements.
Have Suggestions?
We would love to hear your feedback, questions, comments and suggestions. This will help us to make us better and more useful next time.
Share your thoughts and ideas at knowledgecenter@qasource.com

