DevSecOps means security in and around the application, not merely around the application and data. The companies use to implement security at the end of development, which is not a good QA practice.
What is DevSecOps?
DevSecOps means development, security, and operations. It automates and streamlines the platform that integrates security throughout the software development lifecycle. DevOps allows the integration between development and operations, while DevSecOps primary focus is security.
DevOps removes barriers between development and operations teams. In this model, development, and operations teams work together from development and testing to deployment and operations. It focuses on the frequency of delivery, pushing past departmental lines, and calling for collaboration between development and operations for the planning, design, and release of products.
DevSecOps incorporates security techniques like Aqua security, IriusRisk, and SonarQube into the DevOps process. DevSecOps testing helps in overcoming the loopholes and weaknesses that may exist in the development process.
DevOps adds value to software security paradigms. It means security verification becomes a vigorous and integral part of the software development process. In some systems, development teams often push security at the end of the SDLC.
Why Do We Need DevSecOps?
- Security vulnerabilities can exist in open-source software libraries that we import during product development. DevSecOps advocates that security should be applied to the whole product development cycle.
- Developers code on a daily basis and that's why they sometimes skip security checks. DevSecOps brings continuity to securing software deliverables by integrating with the software development process.
- Integrating automated security checks within the continuous integration pipeline will provide you with early warnings and continuously monitor all security vulnerabilities.
- Both unit tests and static code analysis operate closest to ASCII text files and run checks without executing the code. Static code analysis begins before the software testing starts. It helps in identifying the vulnerabilities in the source code.
- Investing in security unit tests and static analyzers will avoid trouble further down the CI pipeline. DevSecOps security testing is crucial for building security into the development process.
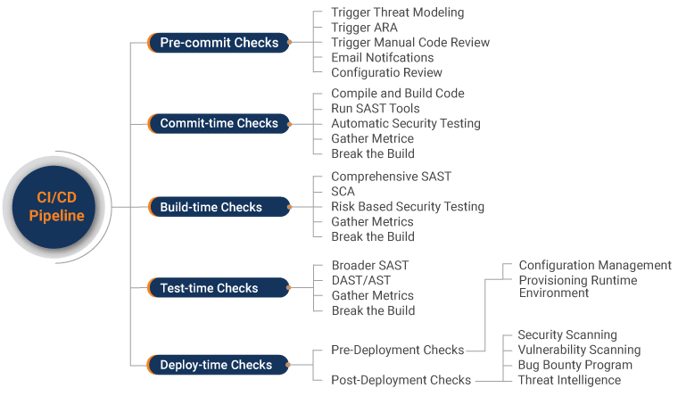
How DevSecOps Works In CI/CD Pipeline?
The following flowchart shows how the CI/CD pipeline process helps in testing and verification of the code:
Benefits of DevSecOps in CI/CD Pipeline
When security measures will be added to the CI/CD pipeline, it adds a layer of security to the CI/CD process. For example, while pushing code to a shared repository like GitHub and sending the notifications to team members, it makes sure that the process is authenticated. If any external library is included within the project, it checks whether it is authentic and licenses risks. Any confidential information like password/credentials is being pushed alongside the code in a VCS. It should notify, before pulling the source code into the CI/CD pipeline environment. Various tools are available for the safety measures to incorporate within the DevOps CI/CD pipeline.
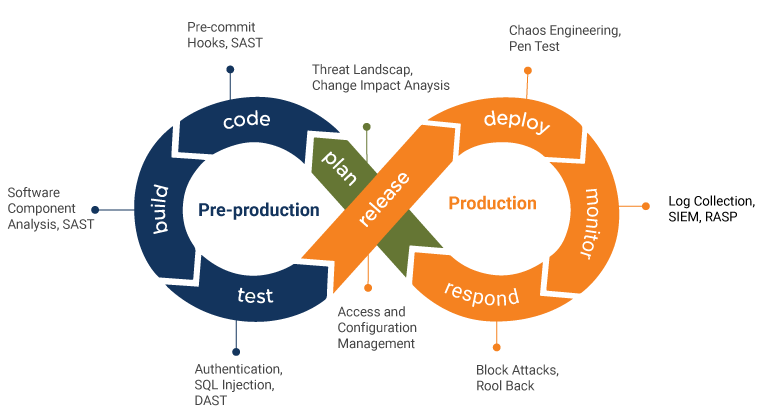
Phases in the DevSecOps Pipeline
The traditional DevOps CI/CD pipeline includes phases like planning, coding, building, testing, releasing, and deploying software. But when working with the DevSecOps process, specific security checks are applied in every phase of the DevOps pipeline.
-
1. Planning
In the planning phase, execute security analysis and create a plan to work out scenarios regarding which security tool can be integrated in different phases.
-
2. Coding
Use linting tools, Git controls, or any other secret manager tool to secure passwords and API Keys. Many vault tools can be used for securing the credentials.
-
3. Building
Use static application testing (SAST) tools to trace down flaws in code before deploying it on production. These tools are specific to programming languages like SpectralOps, Checkmarx, Veracode, Reshift, and Codacy.
-

4. Testing
While testing your application, the dynamic application security testing (DAST) tools can be used to detect errors related to user authentication, authorization, SQL injection, and API-related endpoints. Tools like Invicti (former Netsparker), Acunetix, Indusface WAS, PortSwigger, and Detectify can be used for this.
-
5. Releasing
The safety analysis tools are accustomed to performing vulnerability scanning and penetration testing. These tools should be used just before releasing the new versions. Tools like Clair, Notary, AppScan on the cloud, AWS security service, and ThreatModeler could be used for the same.
-
6. Deployment
After completing the above test in runtime, send a secure infra or build to production for final deployment.
DevSecOps Market Trends
The DevSecOps market is in a rapid growth phase. Also, the DevSecOps automated security testing would play a crucial role in improving the quality and reliability of the development process. The following figures show how DevSecOps market trends have changed till now:
Attractive Opportunities in DevSecOps Market
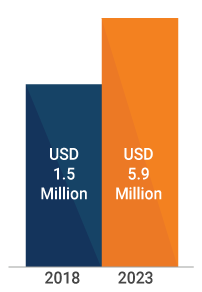
CAGR
31.2%
- Growing needs for highly secure continuous application delivery will drive the growth in DevSecOps market.
- Increase focus on security and compliance to help in adoption of DevSecOps solutions.
- Resistance to adopt new tools and technologies may restrain the growth of the market.
Conclusion
DevSecOps will play a more crucial role as we see a rise in the complexity of enterprise security threats built on modern IT infrastructure. Adopting DevSecOps principles in our continuous pipeline will lower the danger of security vulnerabilities, leading to increased consumer trust in the organization. QASource is one of the leading DevSecOps testing providers that can help you automate security testing in your development process. To know more about DevOps security testing services, contact QASource now.
Have Suggestions?
We would love to hear your feedback, questions, comments and suggestions. This will help us to make us better and more useful next time.
Share your thoughts and ideas at knowledgecenter@qasource.com